Ledger Live Login — Complete Guide to Authentic Access & Secure Crypto Management
Discover how to log into Ledger Live safely, understand the architecture behind Ledger hardware wallets, avoid scams, and manage your digital assets with confidence.
Why Safe Login Matters for Crypto Security
Cryptocurrency offers financial independence, but it also demands responsibility.
When you own your keys, you own your assets — and a single mistake can expose everything.
Ledger hardware wallets are designed to keep private keys offline using cold storage and secure elements, but the software interface must also be used correctly.
Fake login portals, cloned applications, and phishing pages target newcomers daily.
**This guide explains how to log in safely, why Ledger Live remains secure, and how to avoid the most common threats.**
When you own your keys, you own your assets — and a single mistake can expose everything.
Ledger hardware wallets are designed to keep private keys offline using cold storage and secure elements, but the software interface must also be used correctly.
Fake login portals, cloned applications, and phishing pages target newcomers daily.
**This guide explains how to log in safely, why Ledger Live remains secure, and how to avoid the most common threats.**
What Ledger Live Does
Ledger Live is the official companion application used to:
Signing always occurs on the device, making the entire setup resistant to malware, keyloggers, and remote exploitation.
- View balances and portfolios
- Send and receive crypto
- Update firmware
- Access decentralized apps (dApps)
- Manage multiple cryptocurrencies
Signing always occurs on the device, making the entire setup resistant to malware, keyloggers, and remote exploitation.
A Story of a Near Loss
Sophie searched for “Ledger Live login” and clicked a search result labeled “Official Login.”
The site asked her to plug in her device and “verify her recovery phrase.”
Something felt off — because Ledger never requests seed words online.
She closed the page and verified the URL manually.
Had she continued, attackers would have drained her funds instantly.
**This is why using the authentic Ledger Live application is critical — URLs can be spoofed, but official software cannot.**
The site asked her to plug in her device and “verify her recovery phrase.”
Something felt off — because Ledger never requests seed words online.
She closed the page and verified the URL manually.
Had she continued, attackers would have drained her funds instantly.
**This is why using the authentic Ledger Live application is critical — URLs can be spoofed, but official software cannot.**
Secure Login Steps
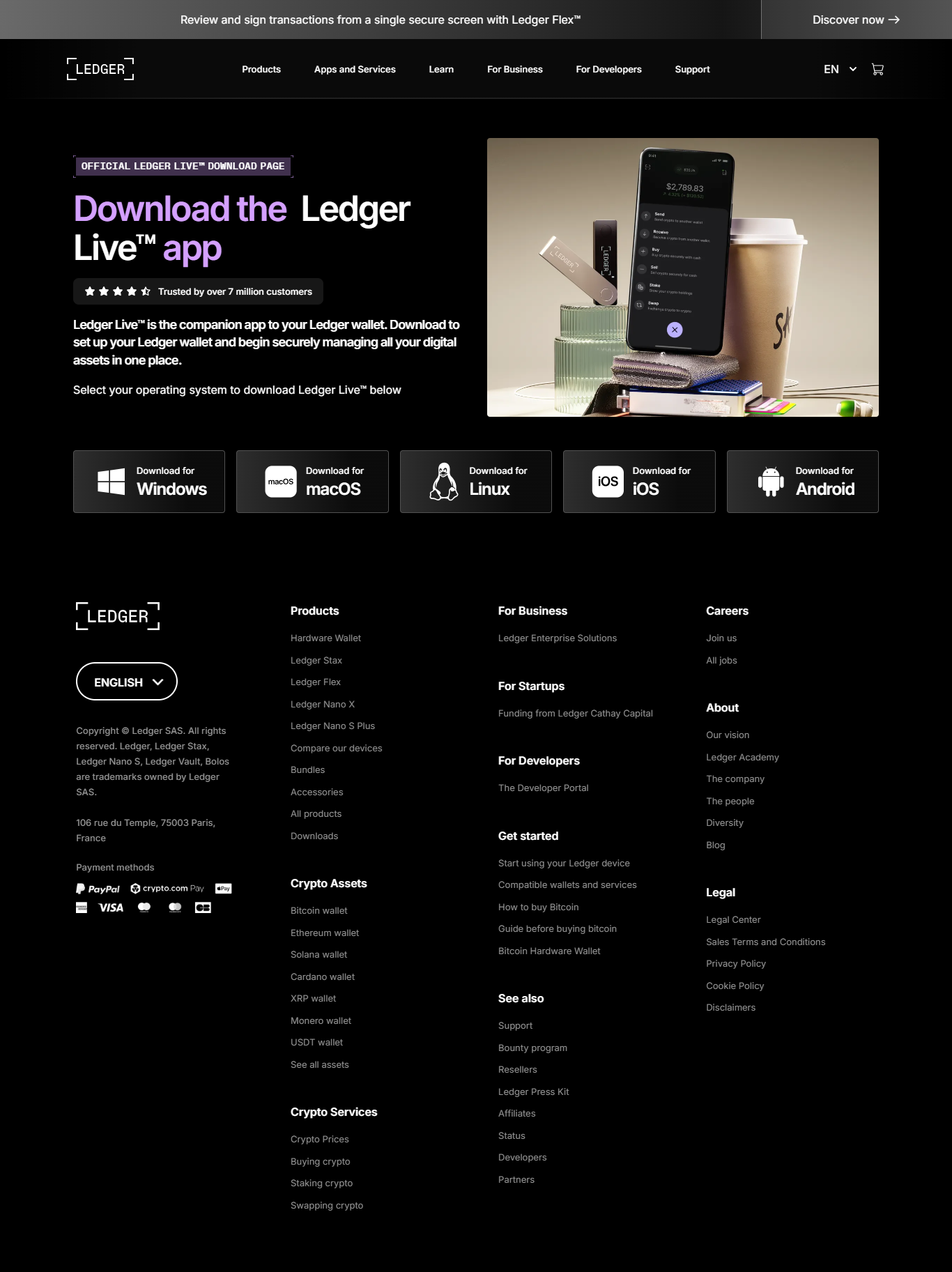
1. Download Ledger Live From Ledger.com
Avoid search engines — fraudulent links often appear above the real one.
2. Install and Launch the Application
Ledger Live works on Windows, macOS, Linux, and mobile.
3. Connect Your Ledger Device
USB for Nano S, Nano S Plus; Bluetooth for Nano X.
4. Enter Your PIN Directly on the Device
Never type the PIN into the computer — authentication is handled by the hardware.
How Ledger Protects Your Keys
Ledger devices rely on:
- Secure elements resistant to tampering
- Offline transaction signing
- Hardware verification screens
- Cold storage isolation
Wallet Comparisons
| Wallet Type | Security | Key Ownership | Use Case |
|---|---|---|---|
| Ledger Hardware Wallet | Very High | User | Cold storage |
| Mobile Wallet | Medium | User | Everyday use |
| Exchange Wallet | Low | Exchange | Trading |
Security Essentials
✔ Only use the official Ledger Live application
✔ Never share your recovery phrase
✔ Keep backups offline
✔ Confirm transactions on device
✔ Avoid unknown plugins
✔ Keep firmware updated
✔ Never share your recovery phrase
✔ Keep backups offline
✔ Confirm transactions on device
✔ Avoid unknown plugins
✔ Keep firmware updated
Frequently Asked Questions
1. Does Ledger Live store keys?
No — keys remain in the device.
2. Is a password required?
No — only the device PIN is used.
3. Can Ledger Live be hacked?
Not in a way that exposes keys because signing remains offline.
4. Does it support multiple coins?
Yes — thousands.
5. What if the device is lost?
Restore using your recovery phrase on a new Ledger.
No — keys remain in the device.
2. Is a password required?
No — only the device PIN is used.
3. Can Ledger Live be hacked?
Not in a way that exposes keys because signing remains offline.
4. Does it support multiple coins?
Yes — thousands.
5. What if the device is lost?
Restore using your recovery phrase on a new Ledger.
Conclusion — Authentic Login Protects Your Wealth
Ledger Live is a powerful tool, but its safety relies on proper usage.
By downloading only official software, authenticating through the physical device, and avoiding suspicious links, you eliminate the most common attack vectors.
Ledger’s architecture — combining cold storage with hardware verification — sets a high standard in self-custody security.
Your assets remain safe when you follow the official path — always log in through the authentic Ledger Live application.
By downloading only official software, authenticating through the physical device, and avoiding suspicious links, you eliminate the most common attack vectors.
Ledger’s architecture — combining cold storage with hardware verification — sets a high standard in self-custody security.
Your assets remain safe when you follow the official path — always log in through the authentic Ledger Live application.